
· 6 min read
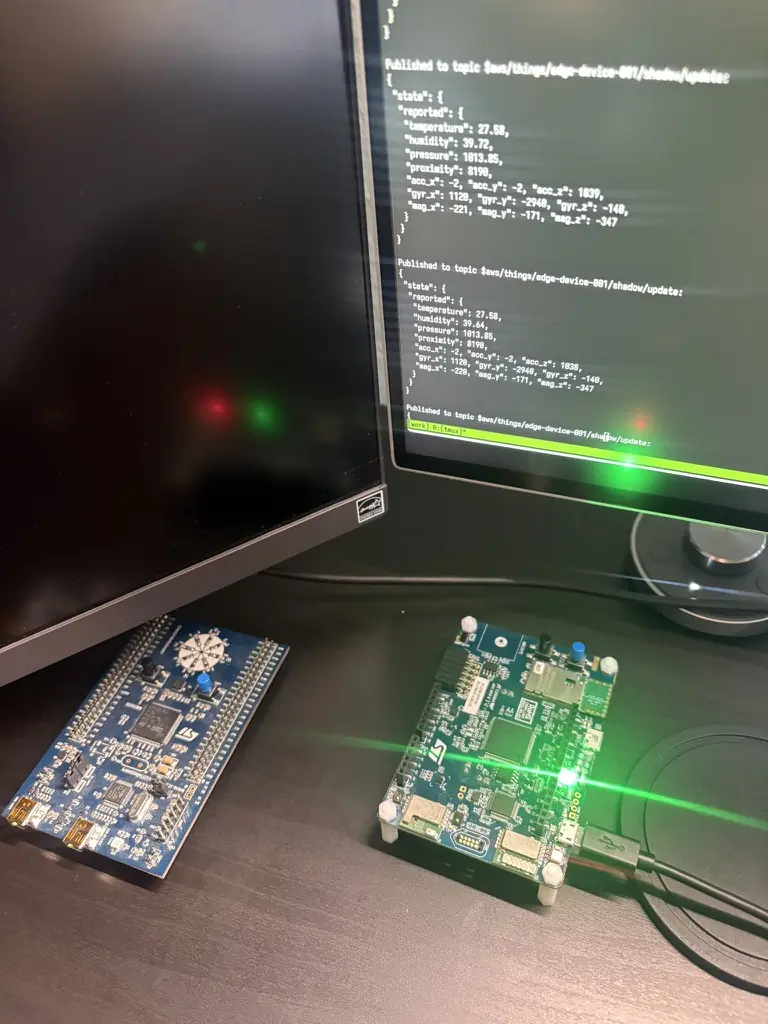
A working note on turning a Rust IoT gateway into an auditable system: preserving telemetry history, making certificate posture visible, and using AI-assisted review to turn runtime evidence into findings a team can act on.
Expertise Proof
These articles show how Combotto reasons from field evidence to audit scope, findings, backlog, and follow-through. The library is listed newest first so recent proof and shipping work stay easiest to find.
Latest blog posts
Newest posts appear first so recent proof and field work stay easiest to scan.
If one of these pressure patterns already matches your system, prefer direct guidance on your current setup: Start with the audit scope conversation.

· 6 min read
A working note on turning a Rust IoT gateway into an auditable system: preserving telemetry history, making certificate posture visible, and using AI-assisted review to turn runtime evidence into findings a team can act on.

· 8 min read
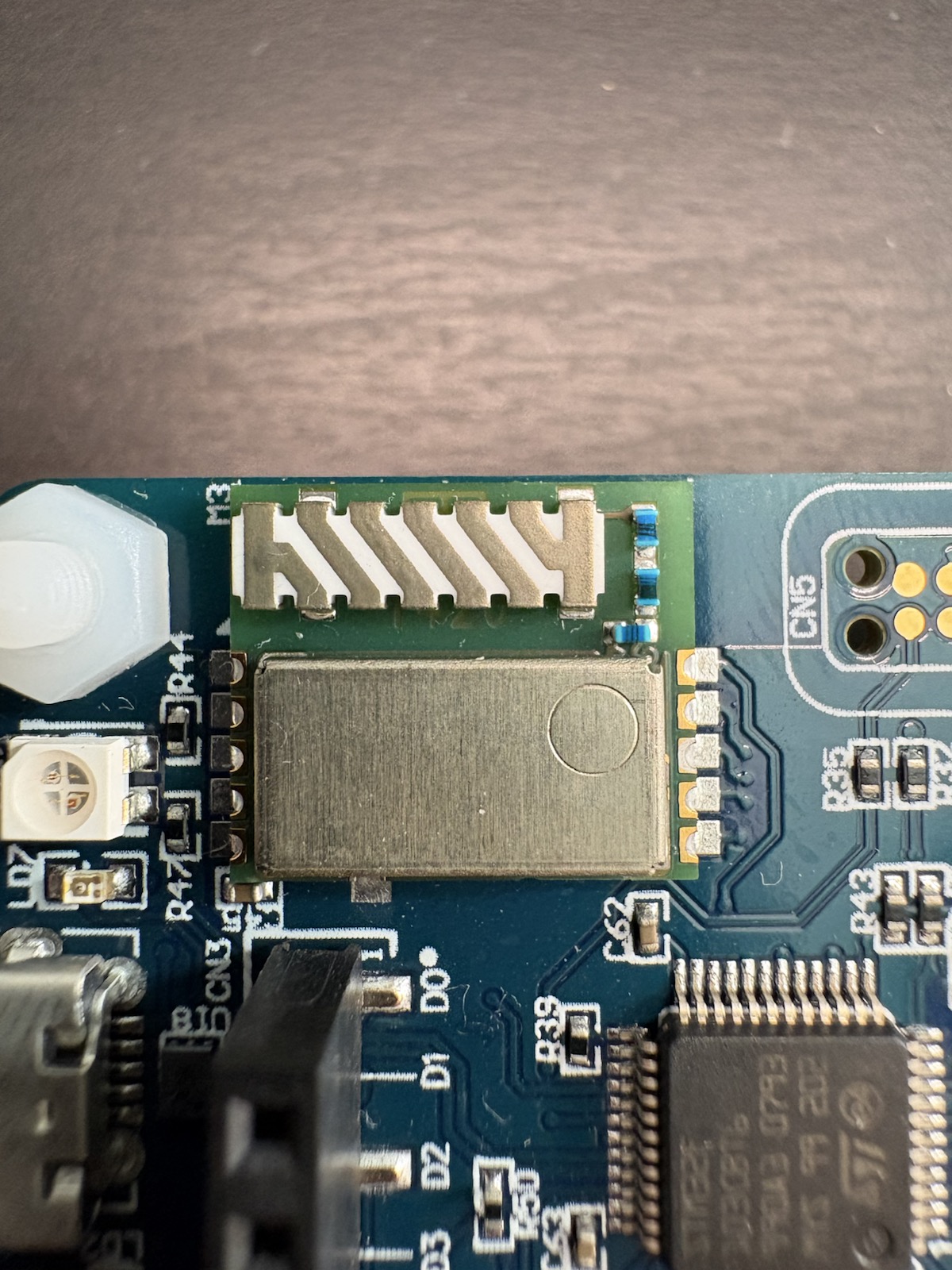
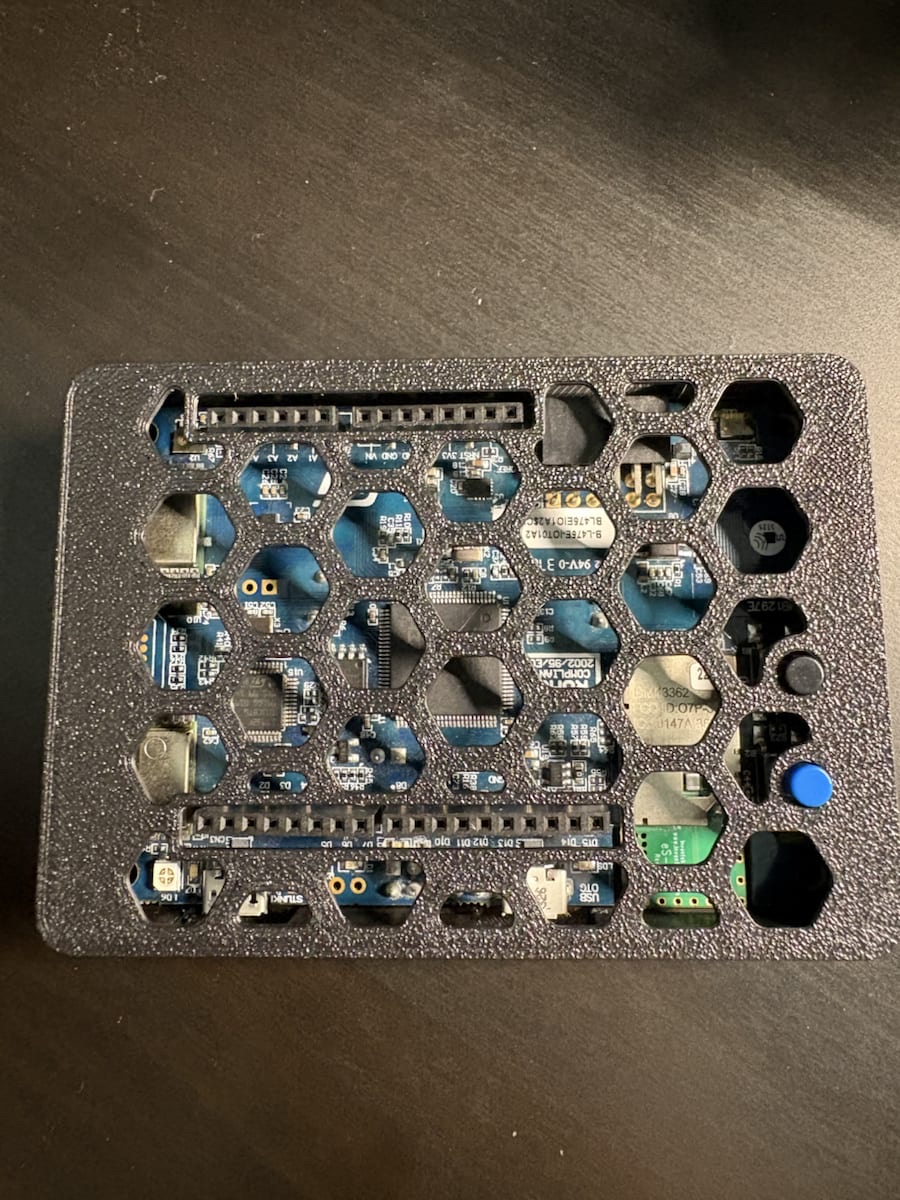
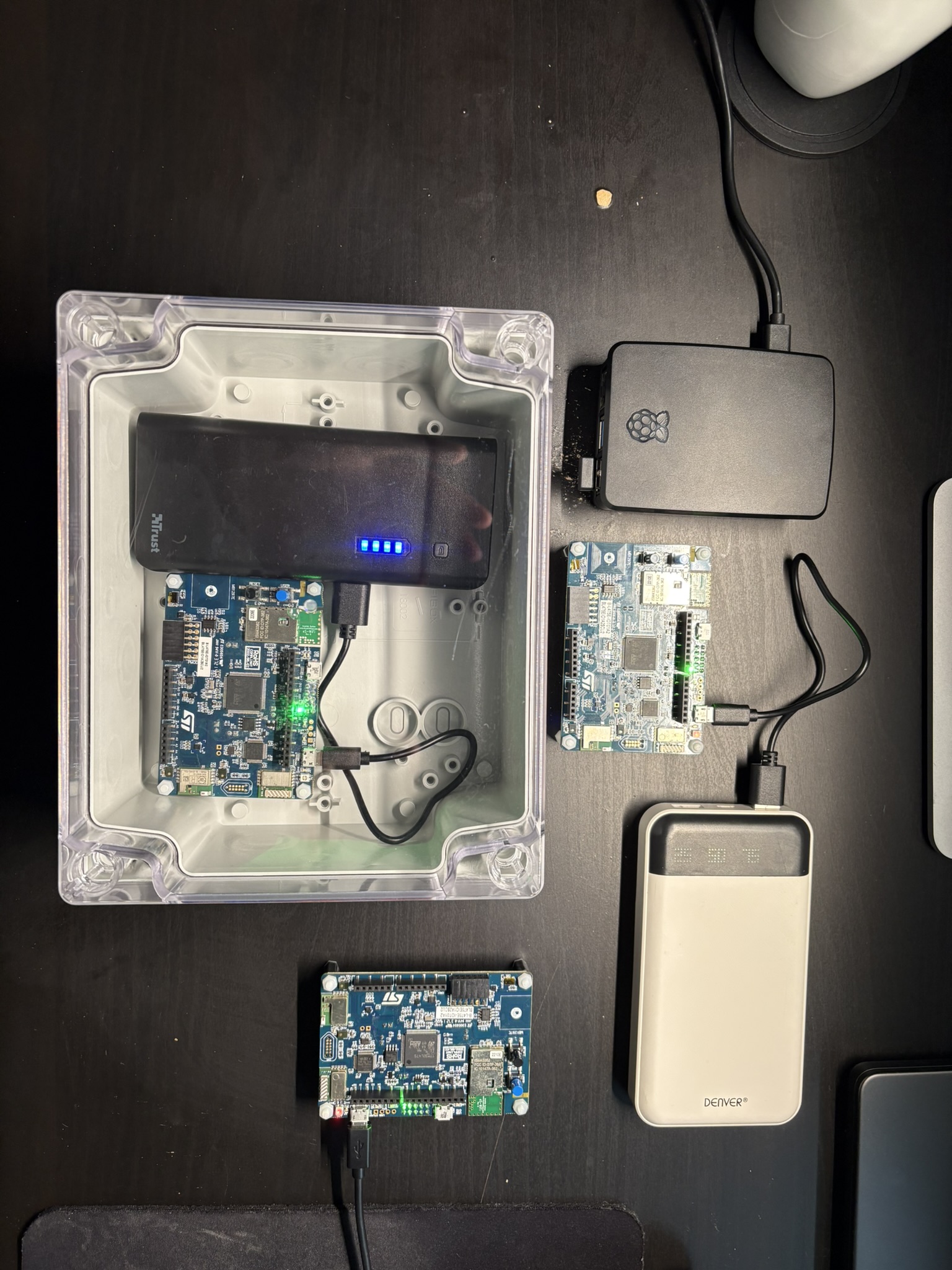
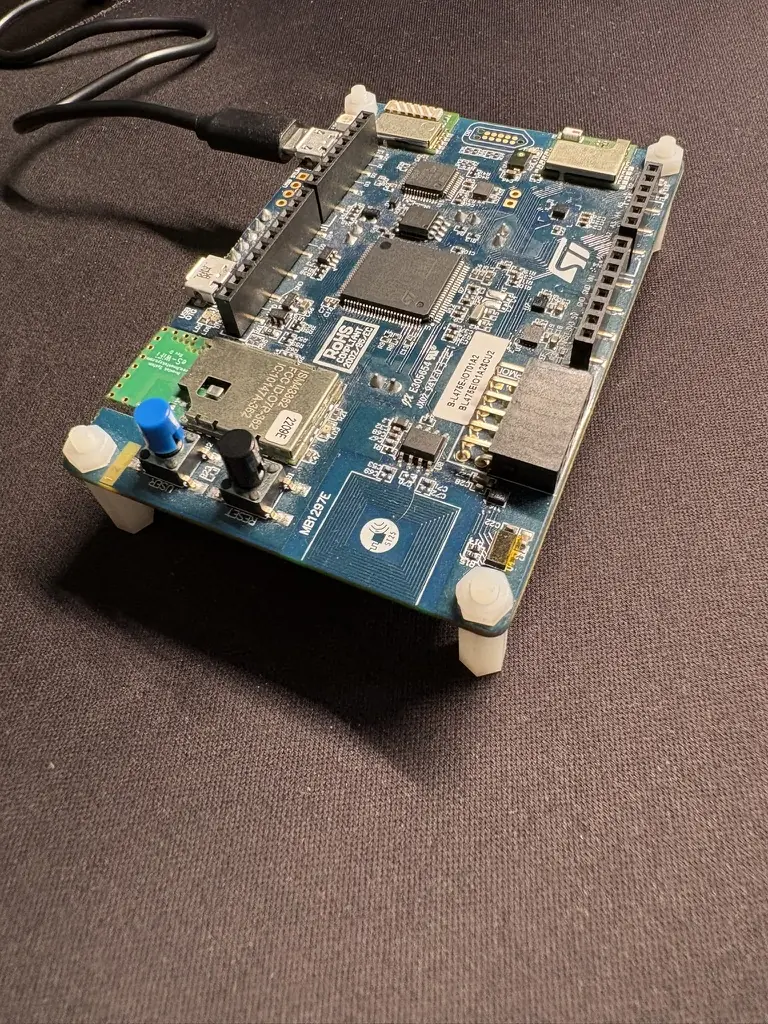
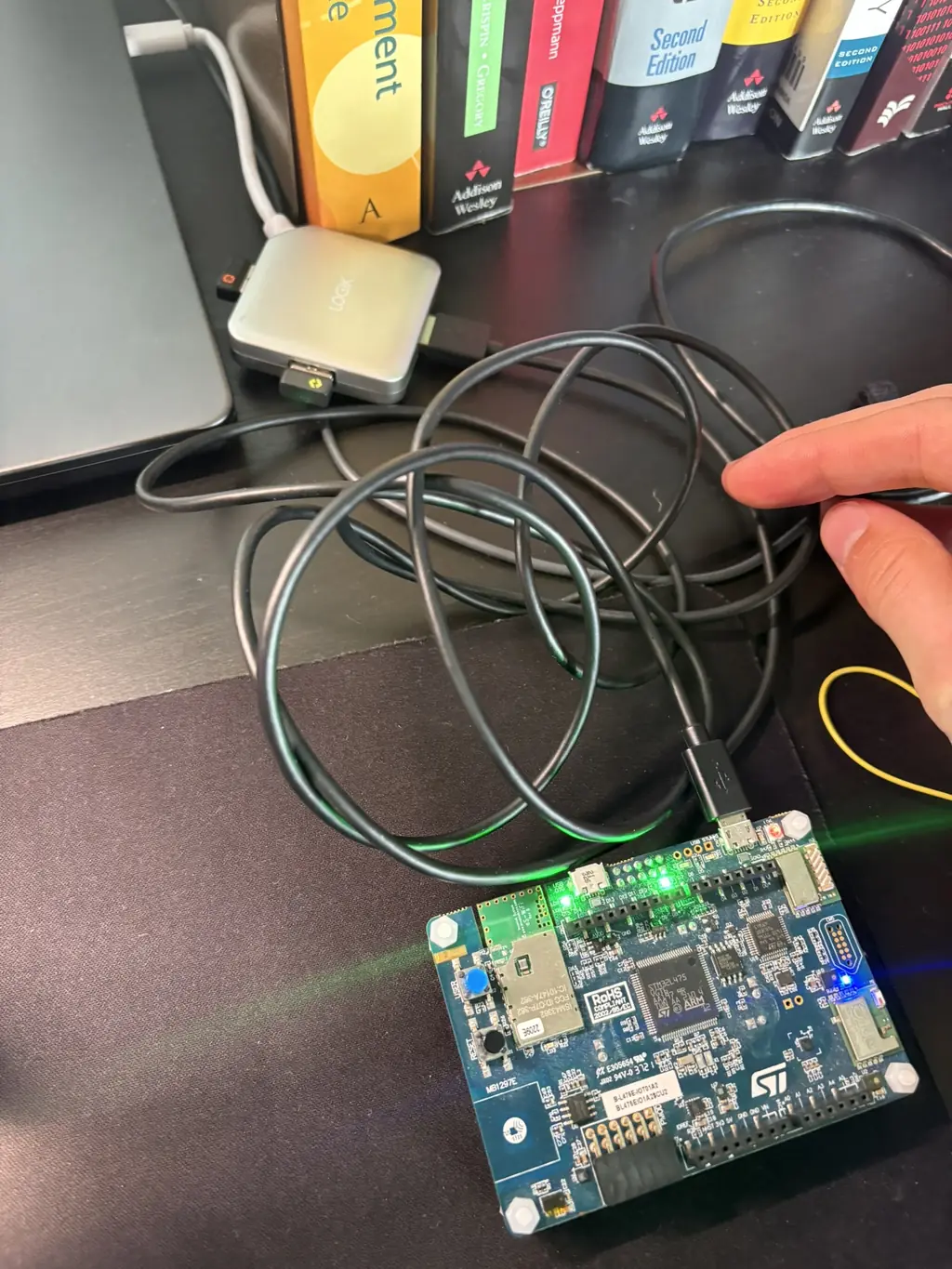
Notes from designing a functional prototype enclosure for the STM32 `B-L475E-IOT01A2` before field testing: which board details mattered, how documentation and real measurements shaped the print, and why service access, transport, and fast reprints mattered more than visual polish.
· 7 min read
A planning note for the next Combotto field demo: two B-L475E-IOT01A2 devices with SPSGRF-868 radios transmitting over 868 MHz, one receiver bridged by serial into a Raspberry Pi 5, and a longer-range telemetry path than Wi-Fi alone usually gives inside and around buildings.
· 7 min read
A practical look at IoT Cyber Resilience Act readiness: public security reporting, release evidence, dependency review, and a clearer path from one serious issue to verified fixes.

· 6 min read
I’m moving my reference IoT gateway from a Dell Linux dev machine to a Raspberry Pi 5 to validate boot, recovery, buffering, and observability on real edge hardware.
· 8 min read
Captured field proof of a Rust IoT gateway on Raspberry Pi 5 handling three STM32 devices over MQTT/TLS, WAL backlog during broker outage, and clean recovery after broker return. Useful for teams evaluating IoT gateway reliability before rollout.

· 8 min read
The Combotto Audit Engine is now ready for pilot projects: canonical reports, run-to-run delta tracking, and alerts for regressions and expiring certificates—built to make Audit → Sprint → Retainer delivery faster and more verifiable.
· 20 min read
What breaks when an edge IoT gateway runs 24/7? Real operational lessons from running a secure edge-to-cloud system under intermittent connectivity, focusing on reliability, observability, and silent failure modes.
· 10 min read
Edge-to-cloud systems without proper observability suffer from slow debugging and reactive incident response. Learn why logs alone fall short and how observability reduces risk.
· 15 min read
I created a structured IoT Architecture Audit Checklist. It captures the core principles of reliability, security, and observability, and provides a consistent process for evaluating device -> gateway -> cloud pipelines.
Next Step
Share the architecture slice, the current risk or delivery pressure, and the decision window. Combotto replies with a fit check, a suggested audit scope, and the clearest next step.